With the increasing reliance on infrastructure in managing IT business which the current health and economic crisis are intensifying, visibility on the IT system is more crucial than ever. Attaining such a level of visibility calls for an evolutive approach to monitoring. That approach involves the capability to track essential ITOps metrics and statuses in real time through a single monitoring console. The best part is that this console is versatile – it’s not stuck to playing just one tune. Take an open source solution such as Graylog: you can easily combine it to your IT monitoring platform for enhanced visibility on your IT system. No more extreme dance moves to keep an eye on both technical and application monitoring. You instantly win the “golden buzzer” for monitoring flexibility – without the neck pains.
Graylog and Centreon: the winning combination for visibility
Graylog is a log management tool offering multiple levels of functionality to meet the needs of application developers, DevOps, and IT Ops teams. With an architecture based on MongoDB and ElasticSearch, large quantities of textual data generated by the various elements of the IT system can be fed and indexed. Graylog helps centralize all application logs, debug applications, manage exceptions and analyze logs.
Centreon, on the other hand, with the help of probes, makes it possible to read log files and to report errors for any given application. This convenient feature is not intended to manage logs on a large scale. Yet log data, correlated with other metrics, are very useful to Centreon users.
According to the State of IT Monitoring carried out by Centreon among 600 IT professionals, companies consider that 39% of the IT system isn’t monitored, on average.
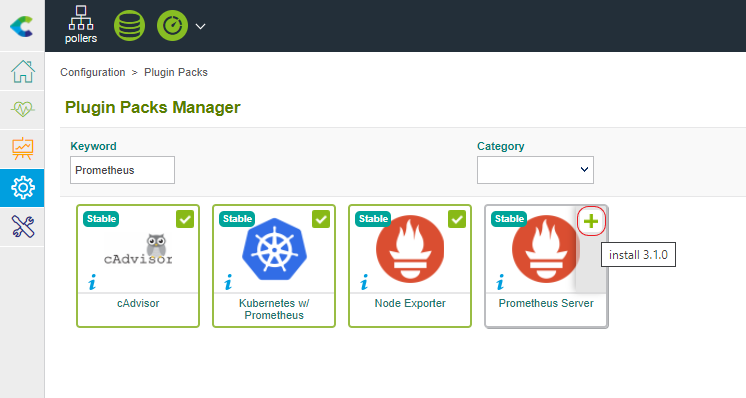
This is where combining Graylog to Centreon becomes a powerful proposition. You can expand performance metrics and statuses for all infrastructure and services by adding the “log” perspective, through implementing the appropriate Plugin Pack.
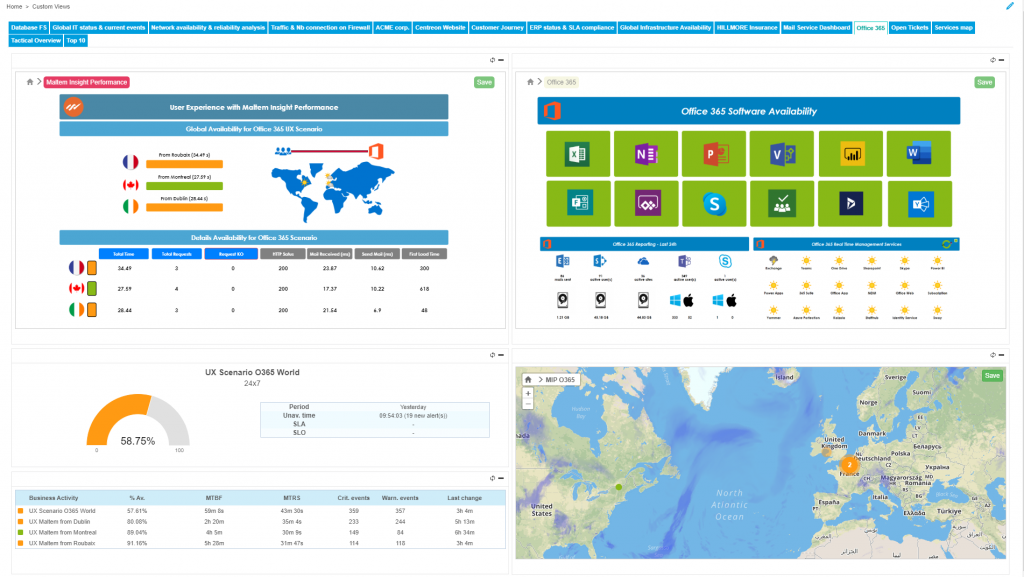
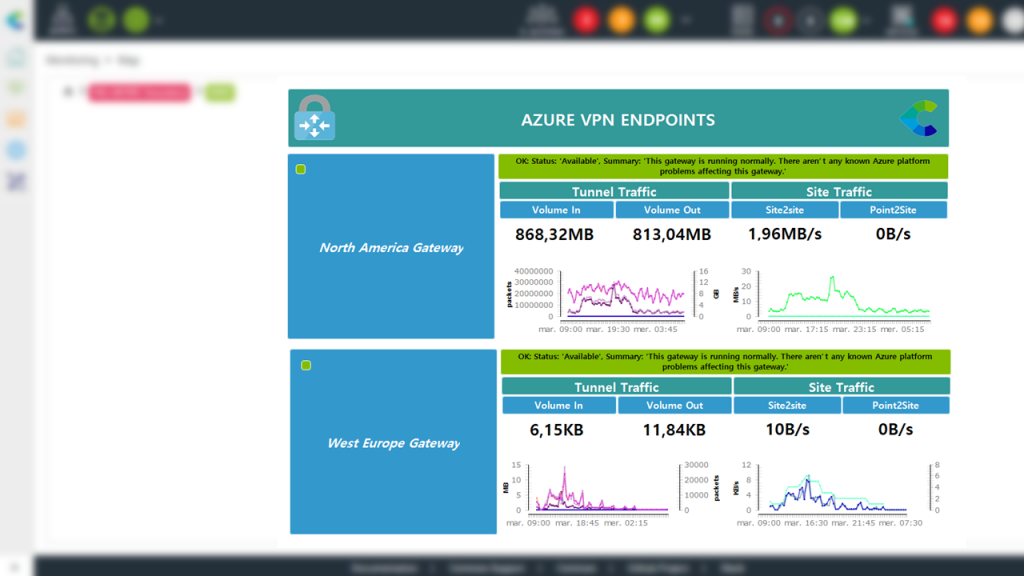
The result: Unified alerts in a single console which can be managed centrally either through Centreon’s native functions or by combining the platform with other solutions.
How to do it: Centralizing operations and alerting in a single console
The main purpose of combining Graylog and Centreon is to make your life easier and allow you to get the best of both solutions in one central location. Centreon will carry out queries in Graylog to extract the essential data that will enrich indicators and alerts in Centreon.
You must already have created dashboards in Graylog, built from more or less complex queries to extract significant information for the health of your IT system. With Centreon’s Graylog Plugin Pack you will be able to use the same syntax as the one used in Graylog by carrying out queries on the API with the Query mode.
Very quickly, by creating a Host using the Graylog Plugin Pack, you will be able to define various requests in terms of services, to retrieve the number of query matches, track their evolution over time and issue alerts when certain thresholds are passed.
The Plugin Pack uses Graylog’s native API to retrieve information quickly and efficiently.
Enriching metrics and alerts for more advanced technical and application KPIs
Use cases for exploiting log consolidation and their correlation with statuses and metrics in Centreon are extensive.
Let’s start with a classic case: by retrieving the number of matches of a simple request such as “http_status:500 AND source:my-website” you can quickly identify if the server supporting your website is generating errors and also set up a graph showing the number of corresponding logs in your Centreon console in order to quickly and visually detect behavior changes in your website (following an update, after adding a new page or feature and so on).
Similarly, using 404 instead of 500 as a filter in a query can give indications of wrong internal or external links generating ‘Pages not found’ for your clients.
You can also identify security uses, for example, by running servers uploading their /var/log/secure logs to Graylog using the Filebeat agent. A basic ‘message: “Failed password’ query can be used to count the number of times a keyword error has occurred on a server, thus detecting a potential dictionary attack.
More generally, by interfacing Graylog with Centreon you can access data from a number of applications that can then be used with Centreon’s service mapping modeling tools. This makes it easier to implement a more application-oriented monitoring in an automated and secure way.
Want to find out more about our Plugin Packs catalog? Access the complete list here.
Would you like to interface Graylog with Centreon? Access the online documentation.